- Winscp Openssh Server Windows
- Winscp Import Openssh Key
- Winscp Ssh Client
- Winscp Openssh Ssh2 Private Key
- Winscp Connect To Openssh Server
SSH sessions permit tunneling network connections by default and there are three types of SSH port forwarding: local, remote and dynamic port forwarding. In this article, we will demonstrate how to quickly and easily set up SSH tunneling or the different types of port forwarding in Linux. Web manual pages are available from OpenBSD for the following commands. These manual pages reflect the latest development release of OpenSSH. Ssh(1) — The basic rlogin/rsh-like client program sshd(8) — The daemon that permits you to log in sshconfig(5) — The client configuration file sshdconfig(5) — The daemon configuration file ssh-agent(1) — An authentication agent that can store.
PuTTY: a free SSH and Telnet client. PuTTY is a free implementation of SSH and Telnet for Windows and Unix platforms, along with an xterm terminal emulator. It is written and maintained primarily by Simon Tatham. The latest version is 0.74. To set the default command shell, first confirm that the OpenSSH installation folder is on the system path. For Windows, the default installation folder is SystemDrive:WindowsDirectory System32 openssh. The following commands shows the current path setting, and add the default OpenSSH installation folder to it.
-->Most authentication in Windows environments is done with a username-password pair.This works well for systems that share a common domain.When working across domains, such as between on-premise and cloud-hosted systems, it becomes vulnerable to brute force intrusions.
By comparison, Linux environments commonly use public-key/private-key pairs to drive authentication which doesn't require the use of guessable passwords.OpenSSH includes tools to help support this, specifically:
- ssh-keygen for generating secure keys
- ssh-agent and ssh-add for securely storing private keys
- scp and sftp to securely copy public key files during initial use of a server
This document provides an overview of how to use these tools on Windows to begin using key authentication with SSH.If you are unfamiliar with SSH key management, we strongly recommend you review NIST document IR 7966 titled 'Security of Interactive and Automated Access Management Using Secure Shell (SSH).' Elizabeth lowell untamed free download.
About key pairs
Key pairs refer to the public and private key files that are used by certain authentication protocols.
SSH public-key authentication uses asymmetric cryptographic algorithms to generate two key files – one 'private' and the other 'public'. English hymnal (uk, 1933)music for your church services. The private key files are the equivalent of a password, and should stay protected under all circumstances. If someone acquires your private key, they can log in as you to any SSH server you have access to. The public key is what is placed on the SSH server, and may be shared without compromising the private key.
When using key authentication with an SSH server, the SSH server and client compare the public keys for username provided against the private key. If the server-side public key cannot be validated against the client-side private key, authentication fails.
Multi-factor authentication may be implemented with key pairs by requiring that a passphrase be supplied when the key pair is generated (see key generation below).During authentication the user is prompted for the passphrase, which is used along with the presence of the private key on the SSH client to authenticate the user.
Host key generation
Public keys have specific ACL requirements that, on Windows, equate to only allowing access to administrators and System.To make this easier,
- The OpenSSHUtils PowerShell module has been created to set the key ACLs properly, and should be installed on the server
- On first use of sshd, the key pair for the host will be automatically generated. If ssh-agent is running, the keys will be automatically added to the local store.
To make key authentication easy with an SSH server, run the following commands from an elevated PowerShell prompt:
Since there is no user associated with the sshd service, the host keys are stored under ProgramDatassh.
User key generation
To use key-based authentication, you first need to generate some public/private key pairs for your client.From PowerShell or cmd, use ssh-keygen to generate some key files.
This should display something like the following (where 'username' is replaced by your user name)
You can hit Enter to accept the default, or specify a path where you'd like your keys to be generated.At this point, you'll be prompted to use a passphrase to encrypt your private key files.The passphrase works with the key file to provide 2-factor authentication.For this example, we are leaving the passphrase empty.
Now you have a public/private ED25519 key pair(the .pub files are public keys and the rest are private keys):
Remember that private key files are the equivalent of a password should be protected the same way you protect your password.To help with that, use ssh-agent to securely store the private keys within a Windows security context, associated with your Windows login.To do that, start the ssh-agent service as Administrator and use ssh-add to store the private key.
After completing these steps, whenever a private key is needed for authentication from this client, ssh-agent will automatically retrieve the local private key and pass it to your SSH client.
Note
It is strongly recommended that you back up your private key to a secure location,then delete it from the local system, after adding it to ssh-agent.The private key cannot be retrieved from the agent.If you lose access to the private key, you would have to create a new key pairand update the public key on all systems you interact with.
Deploying the public key
To use the user key that was created above, the public key needs to be placed on the server into a text file called authorized_keys under usersusername.ssh.The OpenSSH tools include scp, which is a secure file-transfer utility, to help with this.
To move the contents of your public key (~.sshid_ed25519.pub) into a text file called authorized_keys in ~.ssh on your server/host.
This example uses the Repair-AuthorizedKeyPermissions function in the OpenSSHUtils module which was previously installed on the host in the instructions above.
These steps complete the configuration required to use key-based authentication with SSH on Windows.After this, the user can connect to the sshd host from any client that has the private key.
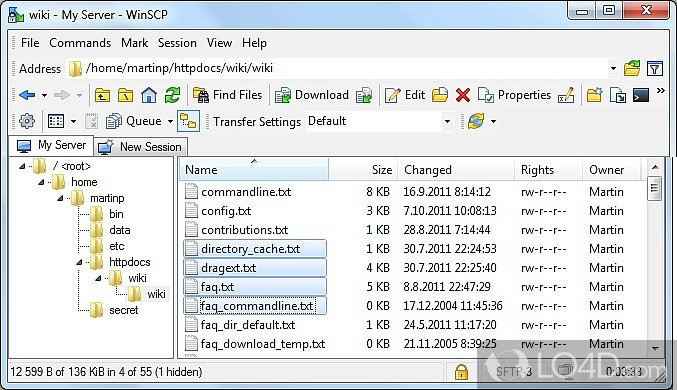
This guide contains description of setting up public key authentication for use with WinSCP. You may want to learn more about public key authentication or SSH keys instead.
- Configure Server to Accept Public Key
Advertisement
Free download 7 zip kommandozeile verschlsseln programs. Before starting you should:
- Have WinSCP installed;
- Know how to connect to the server without public key authentication.
If you do not have a key pair yet, start with generating new key pair.
Connect to your SSH server using WinSCP with the SSH protocol, using other means of authentication than public key, e.g. typically using password authentication.
Once logged in, configure your server to accept your public key. That varies with SSH server software being used. The most common SSH server is OpenSSH.
You can use Session > Install Public Key into Server command on the main window, or Tools > Install Public Key into Server command on SSH > Authentication page page on Advanced Site Settings dialog. The functionality of the command is similar to that of OpenSSH ssh-copy-id command.
Or you can configure the key manually:
- Navigate into a
.sshsubdirectory of your account home directory. You may need to enable showing hidden files to see the directory. If the directory does not exists, you need to create it first. - Once there, open a file
authorized_keysfor editing. Again you may have to create this file, if this is your first key. - Switch to the PuTTYgen window, select all of the text in the Public key for pasting into OpenSSH authorized_keys file box, and copy it to the clipboard (
Ctrl+C). Then, switch back to the editor and insert the data into the open file, making sure it ends up all on one line. Save the file. WinSCP can show you the public key too. - Ensure that your account home directory, your
.sshdirectory and fileauthorized_keysare not group-writable or world-writable. Recommended permissions for.sshdirectory are700. Recommended permissions forauthorized_keysfiles are600. Read more about changing permissions.
There are some specifics when setting up the public key authentication on OpenSSH server on Windows.
- Save a public key file from PuTTYgen, and copy that into the
.ssh2subdirectory of your account home directory. - In the same subdirectory, edit (or create) a file called
authorization. In this file you should put a line likeKey mykey.pub, withmykey.pubreplaced by the name of your key file.
Winscp Openssh Server Windows
For other SSH server software, you should refer to the manual for that server.
Winscp Import Openssh Key
When configuring session, specify path to your private key on SSH > Authentication page of Advanced Site Settings dialog.
Alternatively, load the private key into Pageant.
Winscp Ssh Client
Cloud providers have typically their own mechanism to setup a public key authentication to virtual servers running in the cloud.
For details see guides for connecting to:
Winscp Openssh Ssh2 Private Key
- Amazon EC2;
- Google Compute Engine;
- Microsoft Azure.
Winscp Connect To Openssh Server
- Using public keys for authentication;
- Using PuTTYgen;
- Understanding SSH key pairs.
